CMK version: Checkmk Enterprise Edition 2.1.0p14
OS version: Virtual Appliance 1.5.4
Error message:
When we try to register the new server to checkmk server (through the command “cmk-agent-ctl.exe register”), we received this error:
[2023-01-11 14:48:47.532978 +01:00] ERROR [cmk_agent_ctl] src\main.rs:29: Error pairing with checkmk.intesa.it:8000/Intesa
Caused by:
Request failed with code 500 Internal Server Error: Internal Server Error
We checked the log file inside the checkmk instance and we found this error (inside the logs of agent-receiver) when the client perform the pairing:
[2023-01-11 12:59:07 +0100] [91604] [ERROR] Exception in ASGI application
…
cryptography.x509.base.InvalidVersion: 2 is not a valid CSR version
We checked the source code and we verified that, when client generate the CSR use this code snapshot (file agents/cmk-agent-ctl/src/certs.rs), where it set the version “2”:
pub fn make_csr(cn: &str) -> AnyhowResult<(String, String)> {
// https://github.com/sfackler/rust-openssl/blob/master/openssl/examples/mk_certs.rs
let rsa = Rsa::generate(2048)?;
let key_pair = PKey::from_rsa(rsa)?;
let mut name = X509Name::builder()?;
name.append_entry_by_nid(Nid::COMMONNAME, cn)?;
let name = name.build();
let mut crt_builder = X509Req::builder()?;
crt_builder.set_version(2)?;
crt_builder.set_subject_name(&name)?;
crt_builder.set_pubkey(&key_pair)?;
crt_builder.sign(&key_pair, MessageDigest::sha256())?;
Ok((
String::from_utf8(crt_builder.build().to_pem()?)?,
String::from_utf8(key_pair.private_key_to_pem_pkcs8()?)?,
))
}
but when the agent-receiver verify the request, through the python library “cryptography”, it check the version and if it different of 0 thrown an error:
#[pyo3::prelude::pyfunction]
fn load_der_x509_csr(py: pyo3::Python<'_>, data: &[u8]) -> PyAsn1Result<CertificateSigningRequest> {
let raw = OwnedRawCsr::try_new(data.to_vec(), |data| asn1::parse_single(data))?;
let version = raw.borrow_value().csr_info.version;
if version != 0 {
let x509_module = py.import("cryptography.x509")?;
return Err(PyAsn1Error::from(pyo3::PyErr::from_instance(
x509_module
.getattr(crate::intern!(py, "InvalidVersion"))?
.call1((format!("{} is not a valid CSR version", version), version))?,
)));
}
Ok(CertificateSigningRequest {
raw,
cached_extensions: None,
})
}
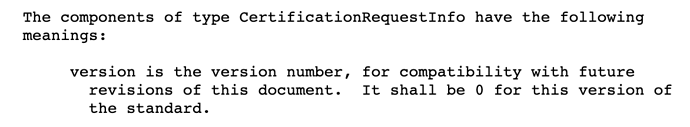
The standard of CSR definition is describe in RFC2986 (https://www.rfc-editor.org/rfc/rfc2986) and affirm that the version of CSR must be 0.
This is a bug of the client cmk-agent-ctl. The client must set the version 0 for the CSR