Hi,
questions mainly for those who run checkmk in real, enterprise production environment. Which platform do you use - Docker/Bare os? But of course all ideas are welcome.
I’ve built environment whole on docker instances with macvlan docker bridge. Main docker instance on one server and 10 docker satellites on 10 different city locations. Now I’m thinking about security and make it secure as much as possible. However documentation is not so complete, I would say about security.
We have nginx reverse proxy as frontend, and from there all traffic is forwarded to multiple docker containers for multiple services. I’ve implemented CA signed certificate into nginx, so when I access URL of my main instance, traffic is over HTTPS, which is good.
However, docker container itself is still listening on HTTP and is accessbile over IP address of container. That’s not good.
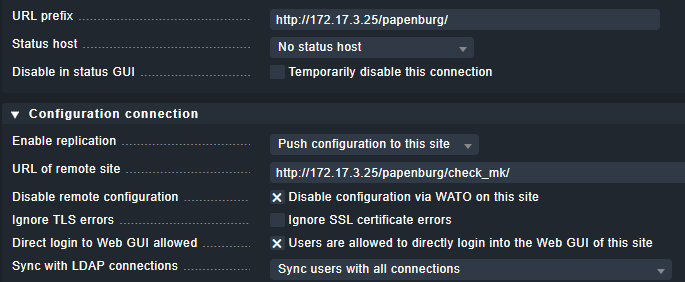
Next, distributed monitoring connections are going over HTTP:
Would be good to make those connections also via HTTPS, right?
Which all steps do I need to do?
And then, docker container of each satellite will still listen on HTTP.
Next thing is to make Agent update over HTTPS. For that I would need create certificate for each satellite and so on. Putting them into container, pretty tricky with persistent volumes, etc.
So at the end, main question. Is Docker environment suitable for enterprise production? With HTTPS/SSL/TLS enabled everywhere it is possbile? I’m starting thinking it is not.
Probably I would re-built environment based on KVM and there install classic check-mk, where I can easily configure Apache’s and work with certificates.
I’m open to all your opinions and ideas.