CMK version:
2.1.0
OS version:
Kubernetes 1.23.1
Error message:
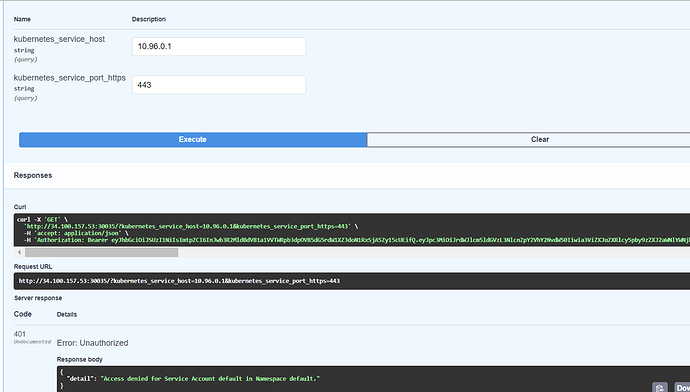
When trying to open checkmk url with external ip of node and node port number, it giving below error
http://34.100.157.53:30035/
{"detail":"Not authenticated"}
I was able to open checkmk application url with version: 2.0.0 when service is exposed as nodePort..However in this case its giving above error..please guide how to solve this issue..
I have followed steps as explained in below video link using helm..
[(247) Episode 26: Monitoring Kubernetes with Checkmk - YouTube](https://www.youtube.com/watch?v=H9AlO98afUE&list=PL8DfRO2DvOK1slgjfTu0hMOnepf1F7ssh&index=29)
All pods are running fine
nigoyal7@master:~/checkmk-2.1.0-helm$ helm upgrade --install --create-namespace -n checkmk-monitor checkmk tribe29/checkmk -f values.yaml
W0528 14:34:04.053908 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
W0528 14:34:04.056895 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
W0528 14:34:04.071334 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
W0528 14:34:04.073938 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
W0528 14:34:04.076297 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
W0528 14:34:04.079906 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
W0528 14:34:04.082159 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
W0528 14:34:04.084740 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
W0528 14:34:04.088943 12396 warnings.go:70] policy/v1beta1 PodSecurityPolicy is deprecated in v1.21+, unavailable in v1.25+
Release "checkmk" has been upgraded. Happy Helming!
NAME: checkmk
LAST DEPLOYED: Sat May 28 14:34:02 2022
NAMESPACE: checkmk-monitor
STATUS: deployed
REVISION: 2
TEST SUITE: None
NOTES:
You can access the checkmk `cluster-collector` via:
NodePort:
export NODE_PORT=$(kubectl get --namespace checkmk-monitor -o jsonpath="{.spec.ports[0].nodePort}" services checkmk-cluster-collector);
export NODE_IP=$(kubectl get nodes --namespace checkmk-monitor -o jsonpath="{.items[0].status.addresses[0].address}");
echo http://$NODE_IP:$NODE_PORT
# Cluster-internal DNS of `cluster-collector`: checkmk-cluster-collector.checkmk-monitor
With the token of the service account named `checkmk-checkmk` in the namespace `checkmk-monitor` you can now issue queries against the `cluster-collector`.
Run the following to fetch its token, resp. ca-certificate:
export TOKEN=$(kubectl get secret $(kubectl get serviceaccount checkmk-checkmk -o=jsonpath='{.secrets[*].name}' -n checkmk-monitor) -n checkmk-monitor -o=jsonpath='{.data.token}' | base64 --decode);
export CA_CRT="$(kubectl get secret $(kubectl get serviceaccount checkmk-checkmk -o=jsonpath='{.secrets[*].name}' -n checkmk-monitor) -n checkmk-monitor -o=jsonpath='{.data.ca\.crt}' | base64 --decode)";
# Note: Quote the variable when echo'ing to preserve proper line breaks: `echo "$CA_CRT"`
To test access you can run:
curl -H "Authorization: Bearer $TOKEN" http://$NODE_IP:$NODE_PORT/metadata | jq
nigoyal7@master:~/checkmk-2.1.0-helm$ export NODE_PORT=$(kubectl get --namespace checkmk-monitor -o jsonpath="{.spec.ports[0].nodePort}" services checkmk-cluster-collector);
nigoyal7@master:~/checkmk-2.1.0-helm$ export NODE_IP=$(kubectl get nodes --namespace checkmk-monitor -o jsonpath="{.items[0].status.addresses[0].address}");
nigoyal7@master:~/checkmk-2.1.0-helm$ export TOKEN=$(kubectl get secret $(kubectl get serviceaccount checkmk-checkmk -o=jsonpath='{.secrets[*].name}' -n checkmk-monitor) -n checkmk-monitor -o=jsonpath='{.data.token}' | base64 --decode);
nigoyal7@master:~/checkmk-2.1.0-helm$ export CA_CRT="$(kubectl get secret $(kubectl get serviceaccount checkmk-checkmk -o=jsonpath='{.secrets[*].name}' -n checkmk-monitor) -n checkmk-monitor -o=jsonpath='{.data.ca\.crt}' | base64 --decode)";
nigoyal7@master:~/checkmk-2.1.0-helm$ echo http://$NODE_IP:$NODE_PORT
http://10.160.0.12:30035
nigoyal7@master:~/checkmk-2.1.0-helm$ curl -H "Authorization: Bearer $TOKEN" http://$NODE_IP:$NODE_PORT/metadata | jq
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 2527 100 2527 0 0 66500 0 --:--:-- --:--:-- --:--:-- 66500
{
"cluster_collector_metadata": {
"node": "worker-1",
"host_name": "checkmk-cluster-collector-f76777f88-7qzwd",
"container_platform": {
"os_name": "alpine",
"os_version": "3.15.0",
"python_version": "3.10.2",
"python_compiler": "GCC 10.3.1 20211027"
},
"checkmk_kube_agent": {
"project_version": "1.0.0"
}
},
"node_collector_metadata": [
{
"node": "worker-3",
"host_name": "checkmk-node-collector-machine-sections-plfwz",
"container_platform": {
"os_name": "alpine",
"os_version": "3.15.0",
"python_version": "3.10.2",
"python_compiler": "GCC 10.3.1 20211027"
},
"checkmk_kube_agent": {
"project_version": "1.0.0"
},
"collector_type": "Machine Sections",
"components": {
"cadvisor_version": null,
"checkmk_agent_version": "2.1.0b1"
}
},
{
"node": "worker-3",
"host_name": "checkmk-node-collector-container-metrics-ljftl",
"container_platform": {
"os_name": "alpine",
"os_version": "3.15.0",
"python_version": "3.10.2",
"python_compiler": "GCC 10.3.1 20211027"
},
"checkmk_kube_agent": {
"project_version": "1.0.0"
},
"collector_type": "Container Metrics",
"components": {
"cadvisor_version": "v0.43.0",
"checkmk_agent_version": null
}
},
{
"node": "worker-2",
"host_name": "checkmk-node-collector-machine-sections-wcxc4",
"container_platform": {
"os_name": "alpine",
"os_version": "3.15.0",
"python_version": "3.10.2",
"python_compiler": "GCC 10.3.1 20211027"
},
"checkmk_kube_agent": {
"project_version": "1.0.0"
},
"collector_type": "Machine Sections",
"components": {
"cadvisor_version": null,
"checkmk_agent_version": "2.1.0b1"
}
},
{
"node": "worker-1",
"host_name": "checkmk-node-collector-machine-sections-jgzrk",
"container_platform": {
"os_name": "alpine",
"os_version": "3.15.0",
"python_version": "3.10.2",
"python_compiler": "GCC 10.3.1 20211027"
},
"checkmk_kube_agent": {
"project_version": "1.0.0"
},
"collector_type": "Machine Sections",
"components": {
"cadvisor_version": null,
"checkmk_agent_version": "2.1.0b1"
}
},
{
"node": "worker-1",
"host_name": "checkmk-node-collector-container-metrics-q8845",
"container_platform": {
"os_name": "alpine",
"os_version": "3.15.0",
"python_version": "3.10.2",
"python_compiler": "GCC 10.3.1 20211027"
},
"checkmk_kube_agent": {
"project_version": "1.0.0"
},
"collector_type": "Container Metrics",
"components": {
"cadvisor_version": "v0.43.0",
"checkmk_agent_version": null
}
},
{
"node": "worker-2",
"host_name": "checkmk-node-collector-container-metrics-bbx9t",
"container_platform": {
"os_name": "alpine",
"os_version": "3.15.0",
"python_version": "3.10.2",
"python_compiler": "GCC 10.3.1 20211027"
},
"checkmk_kube_agent": {
"project_version": "1.0.0"
},
"collector_type": "Container Metrics",
"components": {
"cadvisor_version": "v0.43.0",
"checkmk_agent_version": null
}
}
]
}
nigoyal7@master:~/checkmk-2.1.0-helm$ kubectl get pods -n checkmk-monitor
NAME READY STATUS RESTARTS AGE
checkmk-cluster-collector-f76777f88-7qzwd 1/1 Running 1 (11m ago) 174m
checkmk-node-collector-container-metrics-bbx9t 2/2 Running 0 10m
checkmk-node-collector-container-metrics-ljftl 2/2 Running 0 10m
checkmk-node-collector-container-metrics-q8845 2/2 Running 2 (11m ago) 174m
checkmk-node-collector-machine-sections-jgzrk 1/1 Running 1 (11m ago) 174m
checkmk-node-collector-machine-sections-plfwz 1/1 Running 0 10m
checkmk-node-collector-machine-sections-wcxc4 1/1 Running 0 10m
nigoyal7@master:~/checkmk-2.1.0-helm$
nigoyal7@master:~/checkmk-2.1.0-helm$ kubectl get svc -n checkmk-monitor
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
checkmk-cluster-collector NodePort 10.97.189.177 <none> 8080:30035/TCP 3h9m
Output of “cmk --debug -vvn hostname”: (If it is a problem with checks or plugins)