Hi Heino,
welcome to the Checkmk community! Great question — and a very common situation when migrating from Nagios. The key is understanding that Checkmk offers three different mechanisms for running Nagios-compatible plugins, and each serves a different purpose. Let me break them down:
1. Local Checks — NOT what you need here
You correctly identified the limitation: local checks are executed by the agent without any arguments from the Checkmk server. They are designed for simple scripts that determine their own state directly on the monitored host.
As the docs describe, local checks are called parameterlessly — the script itself contains all logic and thresholds.
Source: Local checks
For your NetApp checks that need -H hostname -w 80 -c 90 style arguments, local checks are the wrong tool.
2. MRPE — Nagios plugins with arguments, executed on the agent host
MRPE (MK’s Remote Plugin Executor) is the direct Checkmk equivalent of Nagios NRPE. It runs the plugin on the monitored host with full argument support.
Configuration in /etc/check_mk/mrpe.cfg:
NetApp_Aggr /usr/local/bin/check_netapp_rest -H 192.168.1.10 -w 80 -c 90
NetApp_Vol /usr/local/bin/check_netapp_rest -H 192.168.1.10 --check volumes -w 70 -c 85
Yes — this means one line per check per host in mrpe.cfg. For many hosts with the same checks, that means many lines. This is the NRPE equivalent: it scales the same way Nagios NRPE scales.
IMPORTANT: Do NOT place Nagios plugins in /usr/lib/check_mk_agent/plugins/ — that directory is reserved for agent plugins. Place them anywhere else (e.g. /usr/local/lib/nagios/plugins/) and reference the full path in mrpe.cfg.
Source: Monitoring Linux - The new agent for Linux in detail (MRPE section)
3. “Integrate Nagios plugins” Ruleset — plugins executed on the Checkmk SERVER (recommended for your NetApp case)
This is the most powerful option for your use case. The plugin runs on the Checkmk server itself — not on the agent host — and you configure it once as a rule that applies to multiple hosts automatically.
Setup:
- Copy the plugin to
~/local/lib/nagios/plugins/ on your Checkmk server
- Make it executable
- Navigate to
Setup > Services > Other services > Integrate Nagios plugins
- Create a rule with the command line, using Checkmk macros:
/path/to/check_netapp_rest -H $HOSTADDRESS$ -w 80 -c 90
Available macros include $HOSTNAME$, $HOSTADDRESS$ and others listed in the inline help of the rule.
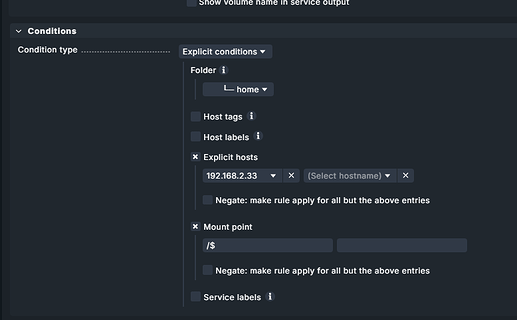
This single rule can apply to an entire host folder or host tag group — so one rule covers all your NetApp systems. No per-host configuration needed.
Note: Active checks behave differently from passive services — they always execute on the Checkmk server, even if the monitored host is DOWN, and they are NOT added via service discovery but generated automatically.
Source: Monitoring network services (Active checks) - Monitoring of HTTPS, TCP, SSH, FTP and further services
Decision summary
| Situation |
Solution |
| Simple script, self-contained logic, no arguments |
Local Check |
| Nagios plugin runs on monitored host, checks a nearby resource (end-to-end) |
MRPE in mrpe.cfg |
| Nagios plugin connects to network device from Checkmk server |
“Integrate Nagios plugins” ruleset |
For check_netapp_rest reaching your NetApp filers from your Checkmk server: Option 3 is the right approach. One rule, all NetApp hosts covered via $HOSTADDRESS$.
For background on all extension options in Checkmk (and why Checkmk recommends against MRPE/Nagios plugins for new developments): Developing extensions for Checkmk
Hope this points you in the right direction!
as hint:
Netapp E-Series Checks - Checkmk Exchange
perhaps @aeckstein can give more info`s
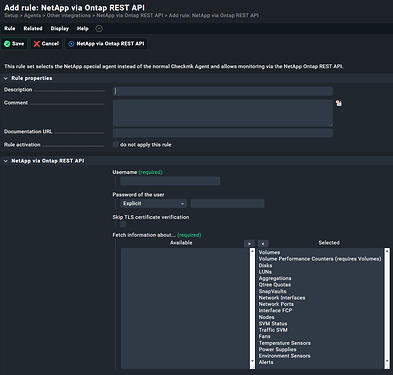
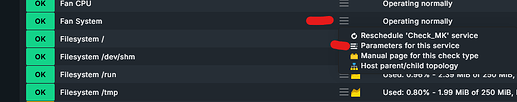
for me the build in works:
![]()
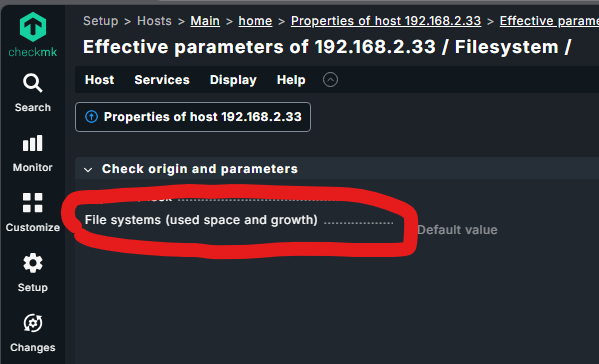
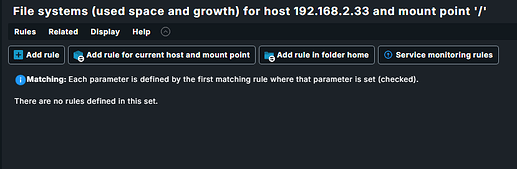
![]() maybe it’s just me…
maybe it’s just me…![]()