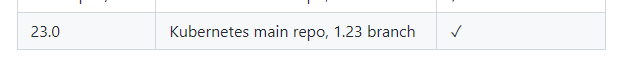
CMK version:
2.0.0p21
OS version:
Debian 11
Error message:
[agent] Version: 2.0.0p21, OS: linux, [special_kubernetes] Agent exited with code 1: (404)
Output of “cmk --debug -vvn hostname”: (If it is a problem with checks or plugins)
[ProgramFetcher] Fetch with cache settings: DefaultAgentFileCache(base_path=PosixPath(’/omd/sites/mhs/tmp/check_mk/data_source_cache/special_kubernetes/MH-K8S-M1’), max_age=MaxAge(checking=0, discovery=120, inventory=120), disabled=False, use_outdated=False, simulation=False)
Not using cache (Does not exist)
[ProgramFetcher] Execute data source
Agent exited with code 1: (404)
Reason: Not Found
HTTP response headers: HTTPHeaderDict({‘Audit-Id’: ‘412628ce-b951-4a8d-9d5f-afb7ae4b21a4’, ‘Cache-Control’: ‘no-cache, private’, ‘Content-Type’: ‘text/plain; charset=utf-8’, ‘X-Content-Type-Options’: ‘nosniff’, ‘X-Kubernetes-Pf-Flowschema-Uid’: ‘a675563a-23a7-4108-8990-ccfa2a5c51cb’, ‘X-Kubernetes-Pf-Prioritylevel-Uid’: ‘7458550b-fa57-48c4-b9a5-365d3b25f1de’, ‘Date’: ‘Mon, 02 May 2022 06:33:22 GMT’, ‘Content-Length’: ‘19’})
HTTP response body: 404 page not found
How I tried to install the agent:
- create service acc. with share/doc/check_mk/treasures/kubernetes/check_mk_rbac.yaml
- Importing certificate
- Storing the password (token) in Checkmk
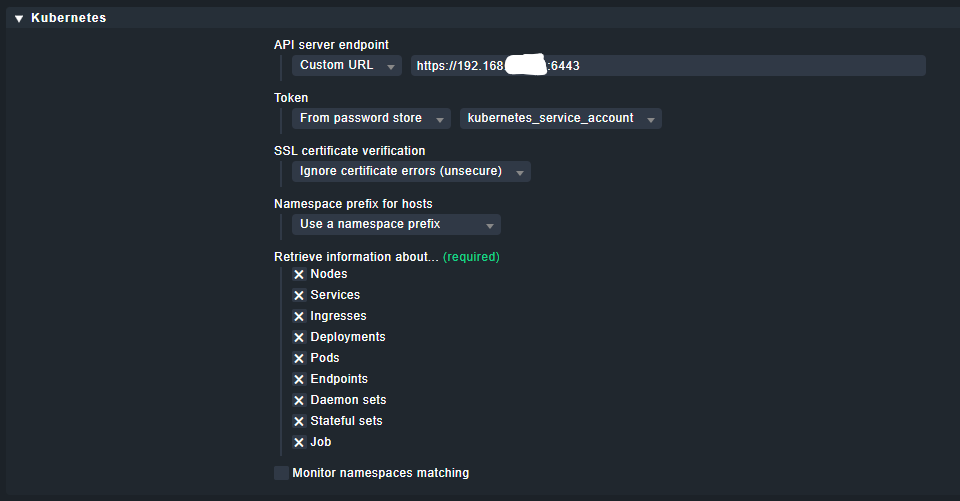
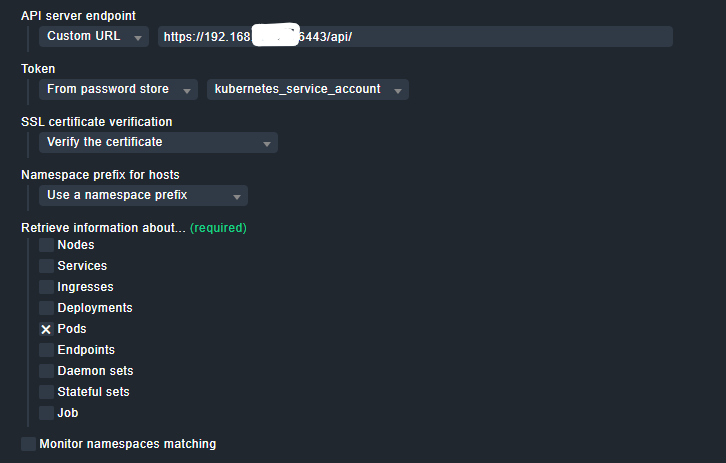
- Adding a Kubernetes cluster to the monitoring
(so all as shown in the docs)
What can’t be wrong:
- Port
- IP ADDRESS
- Token
- Cert