Dear friends of Checkmk,
the new stable release 2.4.0p18 of Checkmk is ready for download.
This stable release ships with 21 changes affecting all editions of Checkmk,
4 changes for the Enterprise editions, 1 Cloud Edition specific and
0 Managed Services Edition specific changes.
Changes in all Checkmk Editions:
Checks & agents
- 19060 Optimized details for clustered services…
- 18552 check_httpv2: Add TLS compatibility mode option…
- 18921 FIX: Check HTTP web service: Fix and improve text searches…
NOTE: Please refer to the migration notes! - 18969 FIX: Cleanup discovered host label files of abandoned hosts…
- 18347 FIX: Clustered services: Fix for disabling services…
- 18700 FIX: Ensure new lines before and after sql based sections in mk_oracle…
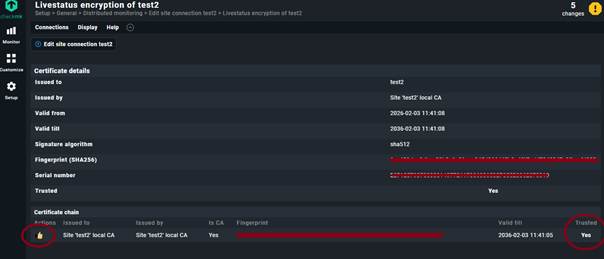
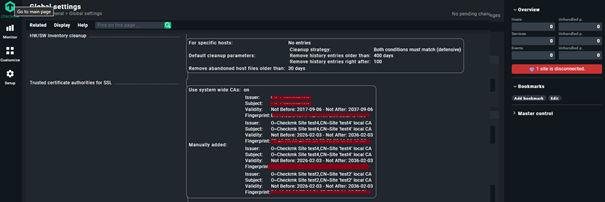
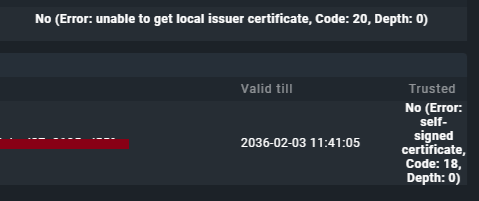
- 18597 FIX: Fix various certificate verification errors for special agents…
- 18947 FIX: Graylog agent configuration: Re-enable macro support for instance field…
- 18732 FIX: Improve service summary for failover aggregated clustered services…
- 18348 FIX: Removed services during bulk discovery…
- 18318 FIX: Solaris agent issue when encryption enabled…
- 18479 FIX: Use fractions of seconds for VSphere System Time Offset…
- 18884 FIX: agent_kube: Abort querying OpenShift endpoint…
- 18596 FIX: kernel_performance: Don’t record negative number of context switches on reboot…
- 18885 FIX: kube: KeyError: ‘user’…
Linux distributions
- 18937 FIX: Expanded System Command Wrappers for OpenSSL Compatibility…
NOTE: Please refer to the migration notes!
Other components
- 19035 SEC: NagVis: Updated to 1.9.48…
Setup
- 19030 SEC: Remote alert handlers (Linux) exposes SSH keys in rule page…
- 18542 FIX: Improve password store management…
- 18910 FIX: Update action: Notification parameters with custom values can now be hashable…
User interface
- 18325 FIX: Graphs: Fix position of indicator line
Changes in the Checkmk Enterprise Edition:
Checks & agents
- 18544 FIX: TCP Fetcher returns error if the host IP can’t be resolved…
- 18886 FIX: mk_oracle: Fix ‘chgrp: cannot access /etc/check_mk/sqlnet.ora: No such file’…
The Checkmk Micro Core
- 19045 FIX: Do not send notifications for soft states…
- 17759 FIX: Fixed removal of non-sticky acknowledgements…
Changes in the Checkmk Cloud Edition:
Checks & agents
- 18703 FIX: Prevent aws_lambda_performance crash on missing metrics…
Changes in the Checkmk Cloud (SaaS):
NO CHANGES
Changes in the Checkmk Managed Services Edition:
NO CHANGES
You can download Checkmk from our download page: Download Checkmk for free | Checkmk
List of all changes: Werks
We greatly thank you for using Checkmk and wish you a successful monitoring,
Your Checkmk Team