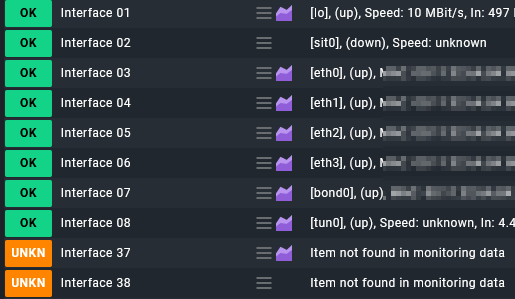
Since an update from server running VPN checkmk suddenly discovers virtual tunnel interfaces that have a short live span and get replaced by a new one with interface nr +1.

I had a rule at first that disables the new ones, but that is not dynamic so I have to keep changing it.
Since all the real interface start with 0, silly me thought, lets negate it instead:
But this results at disabling all services not just the interface nrs not starting with 0. ![]()
I can make a rule that disables services starting with Interface 1, Interface 2 up to Interface 9 for this server, but is there another way?
Can you perhaps disable services based on status detail output so I can filter out services with [tun1000]? If so, how?
I am using raw 2.1.0p5 …